Archive for the ‘Windows Server 2012’ Category
Microsoft Windows Server Update Services (WSUS) – Deserialization Exploit in the Wild (CVE‑2025‑59287)
Montag, Oktober 27th, 2025Microsoft Windows Server 2008 (R2) / 2012 (R2) / 2016 / 2019 / 2022 / 2025 plus Windows 10 / 11 – SPNEGO Extended Negotiation (NEGOEX) Security Mechanism Remote Code Execution Vulnerability
Mittwoch, Juli 9th, 2025 Patches und Workaround verfügbar – es besteht das Risiko demnach nur weil die GPO „Netzwerksicherheit: PKU2U Authentifizierungsanfragen an diesen Computer zur Verwendung von Online Identitäten zulassen“ standardmäßig aktiviert ist sie zu deaktivieren dürfte also vor möglichen Angriffen schützen
Patches und Workaround verfügbar – es besteht das Risiko demnach nur weil die GPO „Netzwerksicherheit: PKU2U Authentifizierungsanfragen an diesen Computer zur Verwendung von Online Identitäten zulassen“ standardmäßig aktiviert ist sie zu deaktivieren dürfte also vor möglichen Angriffen schützen
Microsoft Windows Server 2016 2019 2022 – all users get disconnected approximately every 30-60 minutes and the following is logged in the Application log on the Remote Desktop Gateway
Montag, Juli 29th, 2024 After installing KB5040430 we are seeing issues on the Server 2019 Remote Desktop Gateway on RDS
After installing KB5040430 we are seeing issues on the Server 2019 Remote Desktop Gateway on RDS
Faulting application name: svchost.exe_TSGateway, version: 10.0.17763.3346, time stamp: 0xb6a0daab
Faulting module name: aaedge.dll, version: 10.0.17763.6054, time stamp: 0xce1c5805
Exception code: 0xc0000005
Fault offset: 0x000000000005abe2
Faulting process id: 0x1db0
Faulting application start time: 0x01dad38ae65f65ae
Faulting application path: C:\Windows\system32\svchost.exe
Faulting module path: c:\windows\system32\aaedge.dll
Report Id: bbb10a26-fc25-4bba-9ed8-45c2eff5f5ba
Faulting package full name:
Faulting package-relative application ID:
—
The system was operating normally before the Windows Update
This is now listed as a Known Issue in each relevant KB article:
Windows Server 2022 KB5040437
Windows Server 2019 KB5040430
Windows Server 2016 KB5040434
Microsoft Windows Server 2022 2019 2016 2012 R2 – mit einem wichtigen Out-of-band Update und dieses behebt ein bekanntes Problem das den Lokalen Sicherheitsautoritätssubsystemdienst (LSASS) betrifft
Samstag, März 23rd, 2024 Dieses Update behebt ein bekanntes Problem das den Lokalen Sicherheitsautoritätssubsystemdienst (LSASS) betrifft es kann Speicherverlusten auf Domänencontrollern (DCs) dieses Problem tritt auf nachdem Sie das Update vom 12.03.2024 installiert haben das Leck tritt auf wenn lokale und cloudbasierte Active Directory DCs Kerberos Authentifizierungsanforderungen verarbeiten dieser erhebliche Verlust kann zu einer übermäßigen Speicherauslastung führen aus diesem Fall reagiert LSASS möglicherweise nicht mehr und die DCs werden neu gestartet wenn sie dies nicht erwarten
Dieses Update behebt ein bekanntes Problem das den Lokalen Sicherheitsautoritätssubsystemdienst (LSASS) betrifft es kann Speicherverlusten auf Domänencontrollern (DCs) dieses Problem tritt auf nachdem Sie das Update vom 12.03.2024 installiert haben das Leck tritt auf wenn lokale und cloudbasierte Active Directory DCs Kerberos Authentifizierungsanforderungen verarbeiten dieser erhebliche Verlust kann zu einer übermäßigen Speicherauslastung führen aus diesem Fall reagiert LSASS möglicherweise nicht mehr und die DCs werden neu gestartet wenn sie dies nicht erwarten
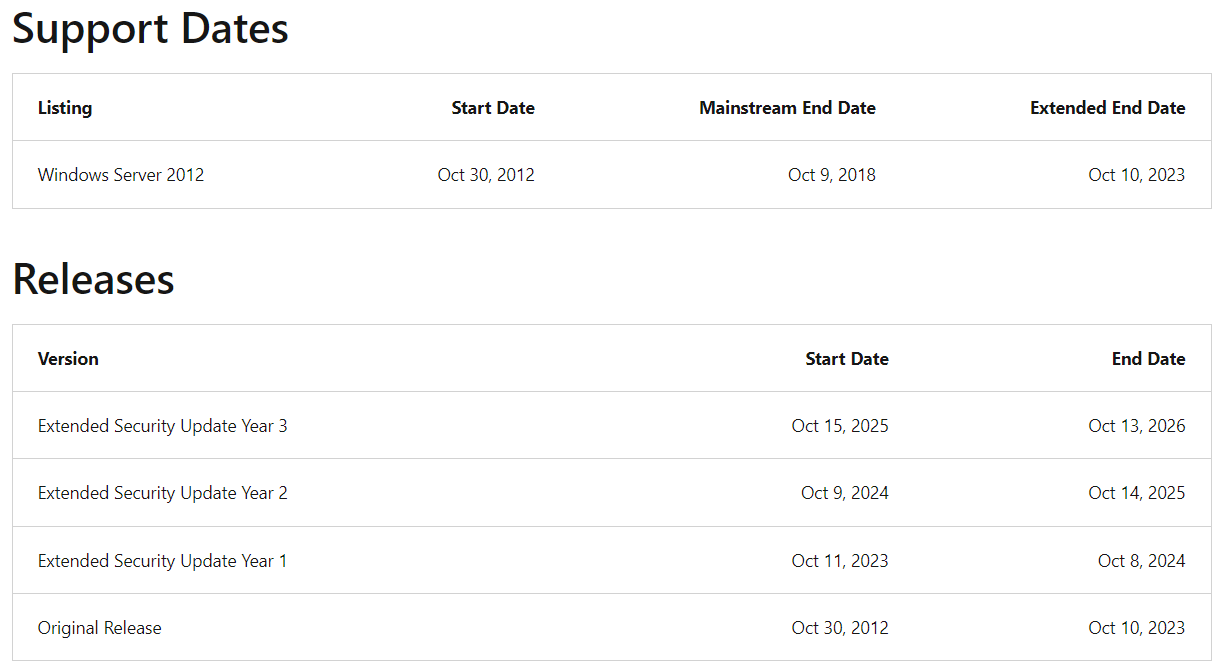
Microsoft Windows Server 2012 ‚Extended Security Update (ESU)‘ – gives administrators an extra three years
Montag, November 13th, 2023Microsoft Windows Server 2012 and its Windows Server 2012 R2 update – today the end of support has been reached
Dienstag, Oktober 10th, 2023
Microsoft Windows Server 2012 and its Windows Server 2012 R2 update – reaching the end of their lifecycles on October 10, 2023
Mittwoch, Oktober 4th, 2023
Microsoft Windows Server 2012 R2 – der erweiterte Microsoft Support endet am 23. Oktober 2023
Sonntag, Januar 1st, 2023
Microsoft Windows Server 2012 2016 2019 – updates released during the November Patch Tuesday that might lead to freezes and restarts on some domain controllers
Samstag, November 26th, 2022 Microsoft Workaround – until a fix is available to address this LSASS memory leak issue a temporary solution allows IT admins to work around domain controller instability
Microsoft Workaround – until a fix is available to address this LSASS memory leak issue a temporary solution allows IT admins to work around domain controller instability
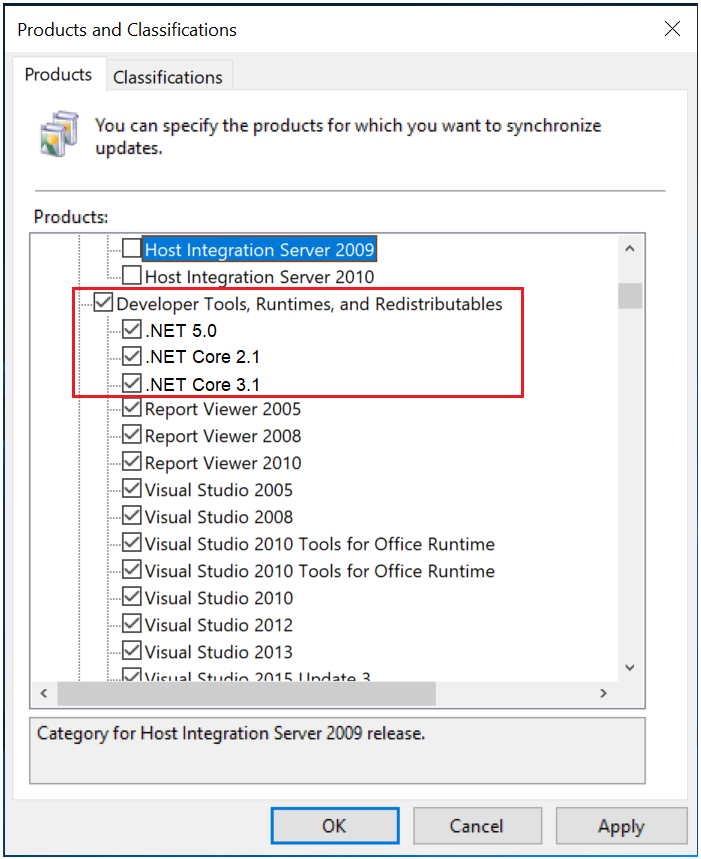
Microsoft .NET Core 2.1 3.1 .NET 5.0 – updates are coming to Microsoft Update
Sonntag, September 18th, 2022 These updates will not be installed via Microsoft Update to computers with a Client operating system that have a supported major/minor version such as .NET Core 2.1, 3.1 or .NET 5.0 already installed
These updates will not be installed via Microsoft Update to computers with a Client operating system that have a supported major/minor version such as .NET Core 2.1, 3.1 or .NET 5.0 already installed
Microsoft .NET Core 2.1 3.1 .NET 5.0 – updates are coming to Microsoft Update
Donnerstag, September 15th, 2022 Configuring Products for synchronization in Windows Server Update Services (WSUS) Products – Updates for .NET Core will be published under .NET Core 2.1 .NET Core 3.1 .NET 5.0 products in WSUS and these products are nested under the Developer Tools Runtimes and Redistributables top level product
Configuring Products for synchronization in Windows Server Update Services (WSUS) Products – Updates for .NET Core will be published under .NET Core 2.1 .NET Core 3.1 .NET 5.0 products in WSUS and these products are nested under the Developer Tools Runtimes and Redistributables top level product
.NET Core Version Registry Key Name Value
Block all .NET Core updates [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NET] “BlockMU” dword:00000001
Block .NET 6.0 updates [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NET\6.0] “BlockMU” dword:00000001
Block .NET 5.0 updates [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NET\5.0] “BlockMU” dword:00000001
Block Core 3.1 updates [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NET\3.1] “BlockMU” dword:00000001
Block Core 2.1 updates [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NET\2.1] “BlockMU” dword:00000001
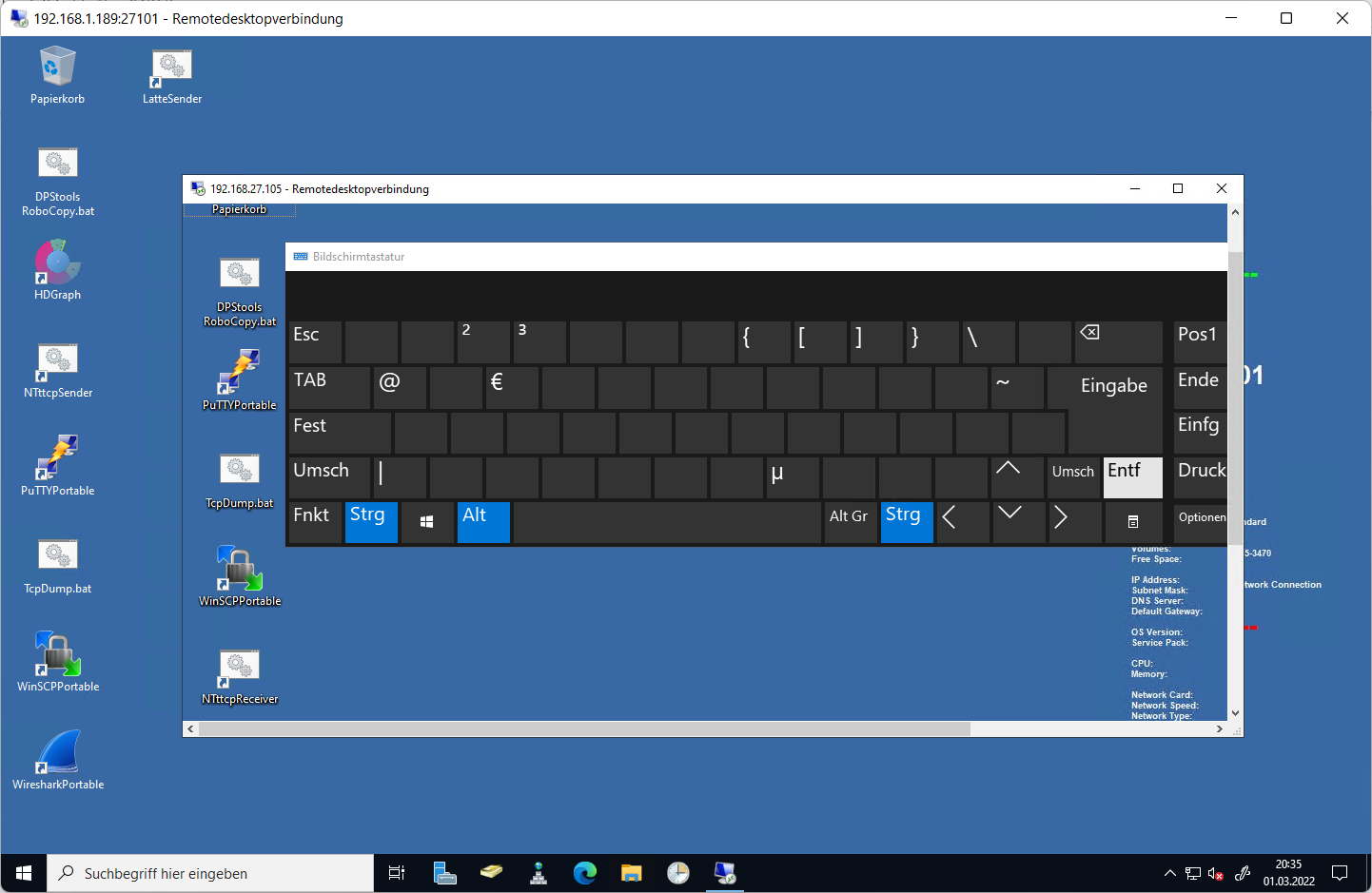
Microsoft Windows Server 2012 2016 2019 2022 – ausführen von STRG+ALT+DEL in einer mehrfachen Remote Desktop Session
Dienstag, März 1st, 2022 Die Bildschirmtastatur (OSK) – ist eine virtuelle Tastatur auf ihrem Bildschirm mit der sie auch ihr Passwort ändern können und so geht’s:
Die Bildschirmtastatur (OSK) – ist eine virtuelle Tastatur auf ihrem Bildschirm mit der sie auch ihr Passwort ändern können und so geht’s:
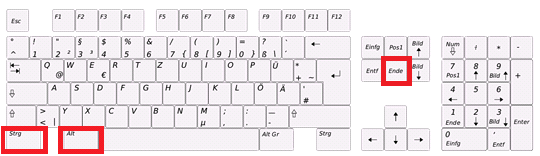
Drücken sie Windows-Taste+R um das Dialogfeld ”Ausführen” aufzurufen geben sie im Dialogfeld ”Ausführen” ‚osk‘ ein und drücken sie die Eingabetaste um die Bildschirmtastatur zu starten halten sie als nächstes die Tastenkombination STRG+ALT auf ihrer physischen Tastatur und klicken sie nun auf die ENTF-Taste mit der OSK Tastatur und minimieren sie die virtuelle Tastatur und klicken sie auf Passwort ändern
Microsoft Windows Server 2012 2016 2019 2022 – ausführen von STRG+ALT+DEL in einer Remote Desktop Session
Donnerstag, Februar 24th, 2022Verwenden Sie STRG+ALT+END anstelle von STRG+ALT+DEL
Apache Guacamole 1.4.0 – is not compatible with the default encryption of Windows if you disable NLA it should work
Mittwoch, Januar 19th, 2022 Apache Guacamole – open the registry editor ‚regedit‘ and make the following settings
Apache Guacamole – open the registry editor ‚regedit‘ and make the following settings
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp]
Change “SecurityLayer” value to dword:00000001
Verify “UserAuthentication” value is dword:0x00000000
This should work without reboot
Microsoft Windows Server 2012 – KB5010797 Out-of-Band-Update 17.01.2022
Dienstag, Januar 18th, 2022 Microsoft Windows Server 2012 – KB5010797 Out-of-Band-Update 17.01.2022
Microsoft Windows Server 2012 – KB5010797 Out-of-Band-Update 17.01.2022